-
DMA Firmware — Custom & Emulated 1:1 Firmware for Vanguard, BattlEye & EAC, Javelin
Full PCIe config space emulation via shadow BRAM and overlay RAM — byte-for-byte donor cloning, TLP compliance, and dedicated driver integration that passes hardware verification from every major kernel-level anti-cheat
-
Featured Products
-
-
DMA firmware is the code flashed onto an FPGA-based PCIe card that rewrites its hardware identity — replacing the stock Xilinx Vendor ID
0x10EEand Device ID0x0666with values cloned from a real consumer device. Without firmware, the card announces itself as what it is: a programmable logic board running pcileech. With properly built firmware, the same card reports as a Wi-Fi adapter, a USB host controller, or a network interface card — and passes hardware verification scans from Vanguard, BattlEye, EasyAntiCheat, and Ricochet.This page explains how DMA firmware works at the engineering level, what anti-cheat systems actually scan for, and why the detection landscape shifted so aggressively through 2025 and into 2026. If you already understand the tech and want to see what we offer, the DMA store has our current firmware packages.
PCIe Configuration Space — Where Detection Starts
Every PCIe device in your system reports its identity through a data structure called Configuration Space. The standard header is 256 bytes. PCIe devices extend this to 4,096 bytes through the Enhanced Configuration Access Mechanism. This structure is not optional — the OS reads it during boot to enumerate hardware, and anti-cheat kernel drivers read it again to look for things that shouldn't be there.
The fields that matter most for detection live in the first 64 bytes. Vendor ID at offset
0x00identifies the chip manufacturer. Device ID at0x02identifies the specific product. Class Code across0x09–0x0Btells the OS what kind of device this is — network controller, audio device, USB host. Subsystem IDs at0x2C–0x2Enarrow it further. Six Base Address Registers at0x10–0x27define the memory windows the device exposes. And the Capabilities Pointer at0x34kicks off a linked list of capability structures — Power Management, MSI/MSI-X, PCIe Express Capability — each chained by next-pointer fields.A raw pcileech FPGA board reports VID
0x10EE(Xilinx) and DID0x0666. That combination has been on every anti-cheat blacklist since BattlEye first started scanning for DMA hardware in 2017. But here's the thing — swapping those two values stopped being enough years ago. The Xilinx PCIe IP core generates internal config space blocks at offsets0x40and0x60that carry a 7-series FPGA fingerprint. EAC has been signing those exact bytes since 2018. Change the VID and DID all you want — the capability structure still screams Xilinx.
Bridge Firmware vs. Emulated Firmware — The Technical Split
The DMA firmware market divides into two tiers based on how deeply the config space is modified. The naming is inconsistent across sellers — "custom," "bridge," "basic," "1:1," "full emu" — but the underlying engineering difference is clear.
Bridge (Custom) Firmware
Bridge firmware patches identity fields through Vivado's PCIe IP core configuration GUI. It replaces VID, DID, Subsystem IDs, Class Code, and sometimes the Device Serial Number. Quick to produce. Works against anti-cheats that only check basic enumeration — standard BattlEye deployments, VAC, FiveM, most server-side systems.
Where it falls apart: the Xilinx IP core generates certain capability blocks internally, and those retain FPGA-specific signatures regardless of what you configure in the GUI. Windows can't find a matching driver for the spoofed identity, so the device shows a yellow exclamation mark in Device Manager. Vanguard's kernel driver has been flipping Bus Master Enable off for driverless devices since 2022 — which kills DMA operations entirely.
Bottom line: bridge firmware against current EAC, ACE, or VGK is a ban waiting to happen.
Emulated (1:1) Firmware
Emulated firmware takes a fundamentally different approach. Instead of patching the IP core's built-in config space, it implements shadow configuration space using Block RAM (BRAM) on the FPGA. The entire 4,096-byte extended config space is stored in BRAM, initialized from a hex dump of a real donor device. When any software — the OS, a driver, an anti-cheat — issues a Configuration Read TLP, the FPGA intercepts it and responds with data from BRAM. The IP core's default registers never get exposed.
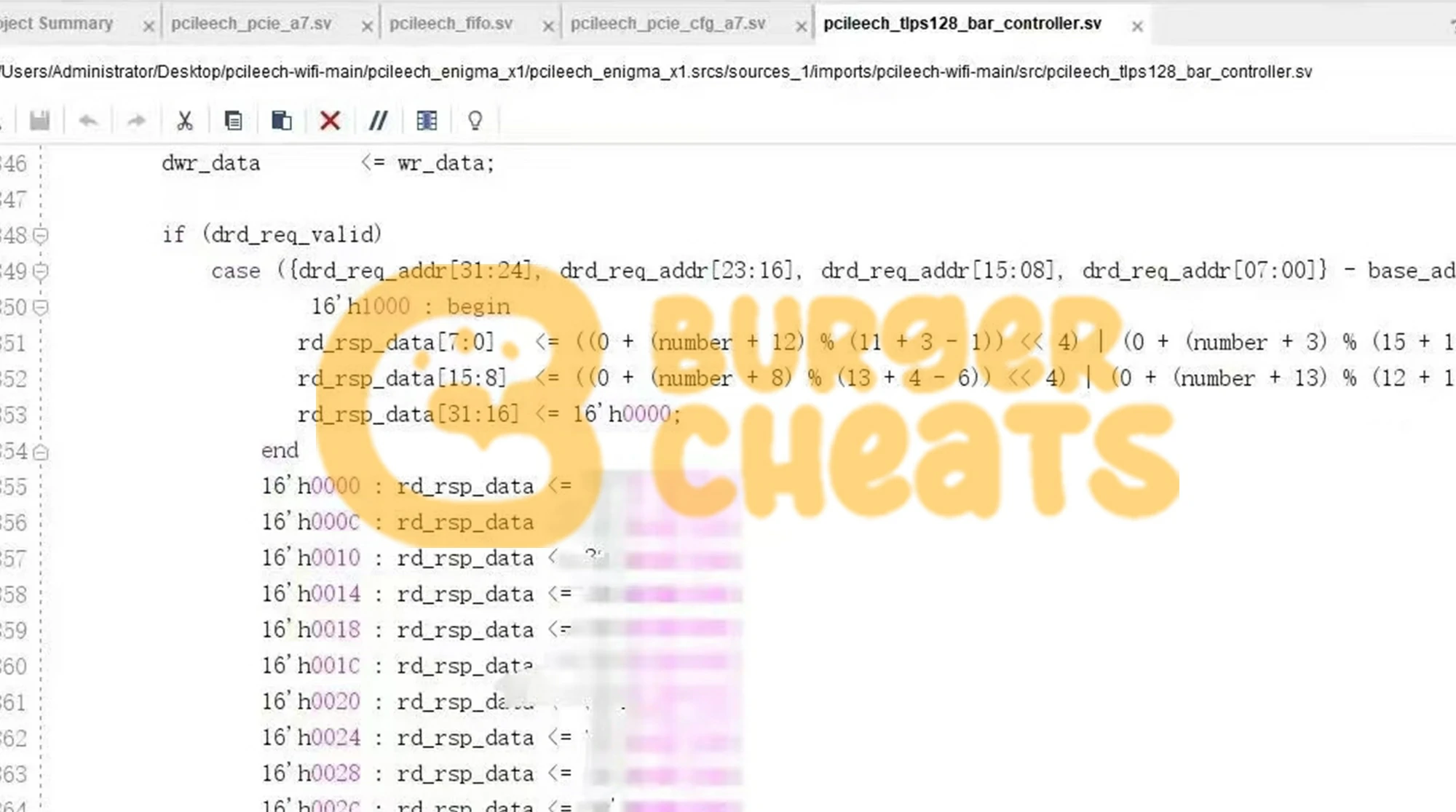
This is where overlay RAM comes in. Real PCIe devices have writable registers — the Command register at
0x04, Status at0x06, BAR addresses, MSI control bits, PCIe Device Control. If the firmware returns correct data on reads but ignores writes, the inconsistency is detectable. EAC deployed shadow config space R/W consistency testing in July 2024 and strengthened it in December 2024. Overlay RAM solves this by maintaining a secondary memory layer for writable fields, merged at read time through a bitmask:(base_value & ~mask) | (overlay_value & mask). Reads and writes stay consistent across every register, matching real silicon behavior.When emulation is complete enough, Windows loads the actual inbox driver for the donor device type. No ⚠️. No "Unknown Device." The anti-cheat sees a fully functional system component. This is the minimum bar for surviving current EAC, ACE (Tencent), and Vanguard scanning — and it's the standard for any firmware worth paying for in 2026.

The Donor Device — Where the Identity Comes From
Every emulated firmware build starts with a donor: a real, physical PCIe card whose complete hardware identity is extracted and cloned. This isn't just the VID/DID — it's the entire 4,096-byte config space, every capability structure in the chain, BAR size masks, interrupt table layouts, extended capabilities (AER, DSN, LTR, VSEC), and the Device Serial Number if the device supports it.
Extraction tools include
lspci -d [VID:DID] -vvv -xxxxon Linux, Arbor or Telescan PE on Windows, and automated solutions like VoltCyclone's PCILeechFWGenerator which uses VFIO passthrough to bind the donor tovfio-pciand dump everything programmatically.Donor selection matters critically. The device must not duplicate any hardware already in the gaming PC — anti-cheats can detect two devices reporting identical identifiers on the same bus. It must be a PCIe x1 device; ACE caught firmware advertising x16 while negotiating x1 as early as 2023.
And here's the part that changed in 2025: anti-cheats now run A/B functionality tests. A card spoofed as a Wi-Fi adapter has to respond to wireless scanning requests. A fake NIC has to handle network packets. A spoofed USB controller has to enumerate child devices. VGK and EAC systematically detected all common donor class spoofs through 2025 — Wi-Fi, NIC, XHCI, audio, capture cards, NVMe. Donor selection in 2026 is a moving target, not a solved problem.

TLP Compliance, BAR Emulation, and Interrupt Generation
Config space emulation gets you past the first scan. Staying undetected under sustained probing requires deeper work.
Transaction Layer Packet Compliance
Anti-cheats send Configuration Read TLPs to extended config space offsets and validate the responses. If the firmware returns all-zeros where real data should exist, or
0xFFFFFFFFfor unmapped regions, the device is exposed. Completion timing matters too — responses from BRAM arrive faster than real silicon, which can itself be a fingerprint. Properly tuned firmware adds latency jitter to match the target FPGA's natural response window.BAR Response Logic
ACE started probing BAR read/write behavior in 2024. When a device claims to have a memory-mapped region at BAR0, the anti-cheat sends Memory Read TLPs to that region and checks whether the responses match expected device behavior. Firmware that doesn't implement PIO (Programmed I/O) response logic for BAR accesses fails these tests. The open-source ekknod/pcileech-wifi project pioneered public BAR PIO support via a dedicated controller that handles one DWORD read and one DWORD write per clock cycle.
MSI Interrupt Generation
VGK's
is_interruptedmechanism, deployed in 2022, validates that devices with MSI capability actually fire interrupts. A network controller that never generates a single interrupt is suspicious. Full emulation firmware implements timer-based or event-driven interrupt generation so the device shows activity matching what the loaded driver expects.This is one of the reasons the 35T FPGA (33,280 logic cells) gets tight on resources for VGK-level profiles — interrupt controller logic, PIO BAR response, overlay RAM, and shadow BRAM all compete for the same silicon.
Read-Only vs. Read-Write DMA — Why It Matters for Detection
DMA cards can both read and write system memory. But from a detection standpoint, these two operations carry very different risk profiles.
Read-only DMA pulls data from game memory without modifying anything. ESP overlays, radar hacks, and player position displays are all read-only — the cheat software on the second PC receives memory data and renders it visually. The gaming PC's memory is never touched. Anti-cheats can't detect read operations through memory integrity checks because nothing was changed.
Read-write DMA is a different story. Writing to the wrong memory region — or a region the anti-cheat is actively monitoring — triggers integrity violations. Aimbot implementations that modify player view angles, no-recoil scripts that zero out recoil vectors, speed hacks that alter movement values: all of these write to game memory and create detectable modifications. VGK's honeypotted memory regions (June 2025) specifically targeted write operations by planting decoy addresses that trigger bans on write access.
Look — this distinction matters when choosing cheat software, not just firmware. The best firmware in the world won't save you if your cheat writes to flagged memory addresses. Serious DMA setups in 2026 lean heavily toward read-only operation for exactly this reason.

How Each Anti-Cheat Detects DMA
Six major anti-cheat systems now actively scan for DMA hardware, each with distinct techniques. Understanding these differences explains why firmware rated for BattlEye might fail against Vanguard — and why "works on all games" is usually a lie.
Vanguard (vgk.sys)
The most aggressive. Loads at system boot (SERVICE_BOOT_START), not at game launch. Bus Master Enable flipping for driverless devices. MSI interrupt validation. Honeypotted memory regions that trap DMA reads (deployed June 2025 — caused a massive ban wave). Full IOMMU enforcement (August 2025). A/B functionality testing across all common donor device classes. UEFI boot integrity verification after the Sleeping Bouncer disclosure. Monthly DMA-targeted ban waves throughout 2025 — January, March, April, June, July, August, and December, each targeting different emulation techniques. Riot's anti-cheat lead stated publicly: Vanguard bans approximately 60,000 accounts per week in Valorant.
BattlEye (BEDaisy.sys)
The first to detect DMA (2017). Config space signature scanning at offsets 0x40 and 0x60. Master abort detection — flags devices that return Unsupported Request completion status. Device history checking via Windows registry. Kernel structure scanning (PiDDBCache, MmUnloadedDrivers). A 2025 ACM paper ("Battling The Eye") provided the first formal security analysis of BattlEye's architecture.
Detection depth varies by game — Escape from Tarkov reportedly runs the most thorough BattlEye configuration, while lighter deployments in games like Hell Let Loose or Squad are less aggressive. Same anti-cheat, different scanning intensity.
EasyAntiCheat
Deployed across 155+ titles. Shadow config space R/W consistency testing (July 2024, strengthened December 2024). Extended capability chain validation. Xilinx 7-series fingerprint scanning. IOMMU enforcement. Thunderbolt enclosure scanning (July 2025). The same kernel driver protects Apex Legends, Rust, Fortnite, The Finals, and Deadlock — though game-specific configurations differ based on developer investment.
Ricochet (Call of Duty)
Took a different path entirely. Instead of deeper local hardware scanning, Ricochet deployed Microsoft Remote Attestation via Azure in November 2025 for Black Ops 7. TPM 2.0 measures each boot step into Platform Configuration Registers. Before ranked play, Ricochet requests an attestation quote, sends it to Azure servers, and receives a cryptographic verdict on whether the boot chain was clean. TPM 2.0 and Secure Boot are now mandatory for Call of Duty and Warzone.
This moves verification entirely outside local control. A compromised kernel can't forge attestation results validated by Microsoft's cloud.
ACE (Tencent Anti-Cheat Expert)
PCIe lane negotiation detection since 2023 (catches x16 spoofed at x1). BAR probing and functional testing since 2024. IOMMU-based "DMA Shield" that remaps memory so unrecognized devices read garbage instead of game data. ACE powers Delta Force, which banned 4,832 accounts in March 2026 with 1,394 flagged specifically for DMA — and issued hardware bans up to 10 years.
EA Javelin (Battlefield 6)
EA's newest kernel-level anti-cheat, built in-house and deployed with Battlefield 6. Like Vanguard, Javelin boots with Windows itself — not at game launch — which means it can catch cheats that try to hook into memory or GPU drivers before the game loads. So aggressive that it conflicts directly with Vanguard: you can't run both simultaneously.
The DMA-relevant details: Javelin requires Secure Boot and TPM 2.0 as mandatory system requirements, with HVCI and VBS listed as additional security features that EA plans to enforce. The system tracks 224 cheat-related programs, hardware solutions, vendors, and resellers. During Open Beta alone, Javelin blocked over 1.2 million cheat attempts, and in December 2025 it prevented 580,000+ more. EA has explicitly stated it will "enforce against cheating hardware" — a direct reference to DMA cards. Javelin reports a 94% overall success rate using its Match Infection Rate (MIR) metric, which counts both confirmed and suspected cheaters per match. This is still a young anti-cheat, but given that it already requires the same OS security stack as Vanguard and Ricochet (Secure Boot + TPM + kernel-level access), expect DMA detection capabilities to deepen rapidly.
The 2025 Detection Timeline — Six Waves That Changed Everything
The myth that DMA hardware is inherently undetectable collapsed through six events in 2025. Each wave exploited a different technical weakness — firmware emulation, IOMMU gaps, UEFI trust assumptions, behavioral patterns. Together, they represent the sharpest escalation in the nine-year history of DMA vs. anti-cheat.
March–May: Ditto ban wave. The Ditto PCIe emulator — a subscription-based framework that could emulate any of 11,000+ device types — was detected sequentially by Vanguard (March), EAC (April), and FACEIT (May). The developer went unreachable. Resellers couldn't recover funds. Thousands of accounts across Valorant, Fortnite, and Apex went down.
June: IOMMU + honeypot double wave. Two simultaneous strikes. ACE's IOMMU detection caught standard DMA cards and $4,500 MITM passthrough devices alike — IOMMU doesn't care how expensive your hardware is. Simultaneously, Vanguard deployed honeypotted memory regions: decoy addresses planted in game memory that only DMA readers would touch. Reading them = instant ban.
August: PUBG Zakynthos wave. Over 30,000 accounts banned for DMA in a single month. 17.6% of all PUBG bans that week. Total DMA bans in PUBG exceeded 80,000.
September: CS2 "VAC 3.0." Valve silently deployed a massive VAC Live update. Dozens of cheat providers reported detection. Whether user-level VAC can directly detect DMA hardware remains debated — many analysts attribute the improvement to VACnet's behavioral AI rather than hardware scanning.
December: Sleeping Bouncer. Riot's researchers discovered UEFI firmware across ASUS, Gigabyte, MSI, and ASRock was falsely reporting Pre-Boot DMA Protection as active when IOMMU wasn't initialized during early boot (CVE-2025-11901 through CVE-2025-14304, all CVSS 7.0). All four manufacturers released BIOS patches. VGK now blocks Valorant on unpatched boards. First time anti-cheat research prompted industry-wide motherboard firmware updates.

The DMA Hardware Stack — From FPGA to Fuser
Understanding the full setup chain helps you see where firmware fits — and where the other detection surfaces are.
The DMA card sits in the gaming PC's PCIe slot, running firmware that disguises it as legitimate hardware. Xilinx Artix-7 FPGAs dominate: the XC7A35T (33,280 logic cells, entry-level), XC7A75T (75,520 logic cells, most popular), and XC7A100T (101,440 logic cells, high-end). More logic cells means more room for shadow BRAM, overlay RAM, PIO response logic, and interrupt controllers. A USB-C cable connects the DMA card to a second PC running the cheat software — the core premise being that no cheat code executes on the monitored gaming machine.
A KMBox or Makcu injects mouse movements back into the gaming PC for aimbot functionality. The KMBox NET (~$50–80) uses 100M Ethernet at ~1,000 calls/second. The open-source Makcu (dual ESP32-S3, ~$20–40) uses true USB passthrough with sub-700μs command latency — the recommended choice in 2026. The older KMBox B+ Pro is being phased out due to higher detection risk.
A fuser combines two video signals — game feed from the gaming PC, ESP overlay from the cheat PC — onto one monitor. DICHEN dominates manufacturing: their 6th-gen HDMI fuser handles 2K@144Hz, the DC500 handles 4K@160Hz.
Need hardware guidance? Our DMA hardware page covers card selection, fuser models, and the KMBox vs. Makcu comparison in detail.
Three Developments That Shifted the Landscape
2025 didn't just add new detection methods — it changed what "undetected" means at a fundamental level.
IOMMU Enforcement
Input/Output Memory Management Unit hardware has existed for years, but anti-cheats only started actively requiring and verifying it in mid-2025. When IOMMU is properly configured, it maps which PCIe devices can access which physical memory addresses. An unrecognized DMA card requesting access to game memory gets blocked — not detected, blocked. The difference matters: detection lets you keep playing until the ban wave; IOMMU stops the cheat from functioning at all.
FACEIT requires IOMMU for players above 3,000 Elo. Fortnite mandates it for all PC tournaments since February 2026. VGK and ACE enforce it for all players. This is the single most impactful defense deployed in 2025.
The Sleeping Bouncer and UEFI Auditing
Riot's researchers found that UEFI firmware across all four major motherboard manufacturers was lying about DMA protection status during early boot. The resulting CVEs and mandatory BIOS patches represent something new: anti-cheat vendors auditing hardware manufacturer firmware and demanding fixes. The gaming industry is now driving UEFI security improvements. If you play Valorant and haven't updated your BIOS since late 2025, you need to — regardless of which DMA firmware you run.
Remote Attestation via TPM 2.0
Ricochet's Azure-based implementation validates the entire boot chain through Microsoft's cloud infrastructure. A compromised local system cannot forge the attestation result. This doesn't detect DMA cards directly — it verifies that the system hasn't been tampered with to enable them. Combined with Secure Boot and VBS (Virtualization-Based Security), it creates a chain of trust from hardware initialization through OS runtime.
The community's response? Bootkits and hypervisors to bypass IOMMU — which defeats the entire point of external DMA (no software on the gaming PC) and introduces real security risks from unsigned kernel code. Let's be real: when the workaround for your workaround requires compromising your own system, the arms race has shifted in the defender's favor.
The pcileech Foundation — Every Firmware's Origin
Virtually all commercial DMA firmware traces its lineage to a single open-source project: pcileech-fpga, created by Swedish security researcher Ulf Frisk in 2016 and released under MIT license (~1,700 GitHub stars). The repository provides HDL code for FPGA devices that achieve full 64-bit physical memory access via raw PCIe Transaction Layer Packets. The companion software stack — pcileech for direct DMA operations, LeechCore for abstracted memory access, MemProcFS for mapping target memory as a virtual filesystem — is the foundation every cheat developer builds on.
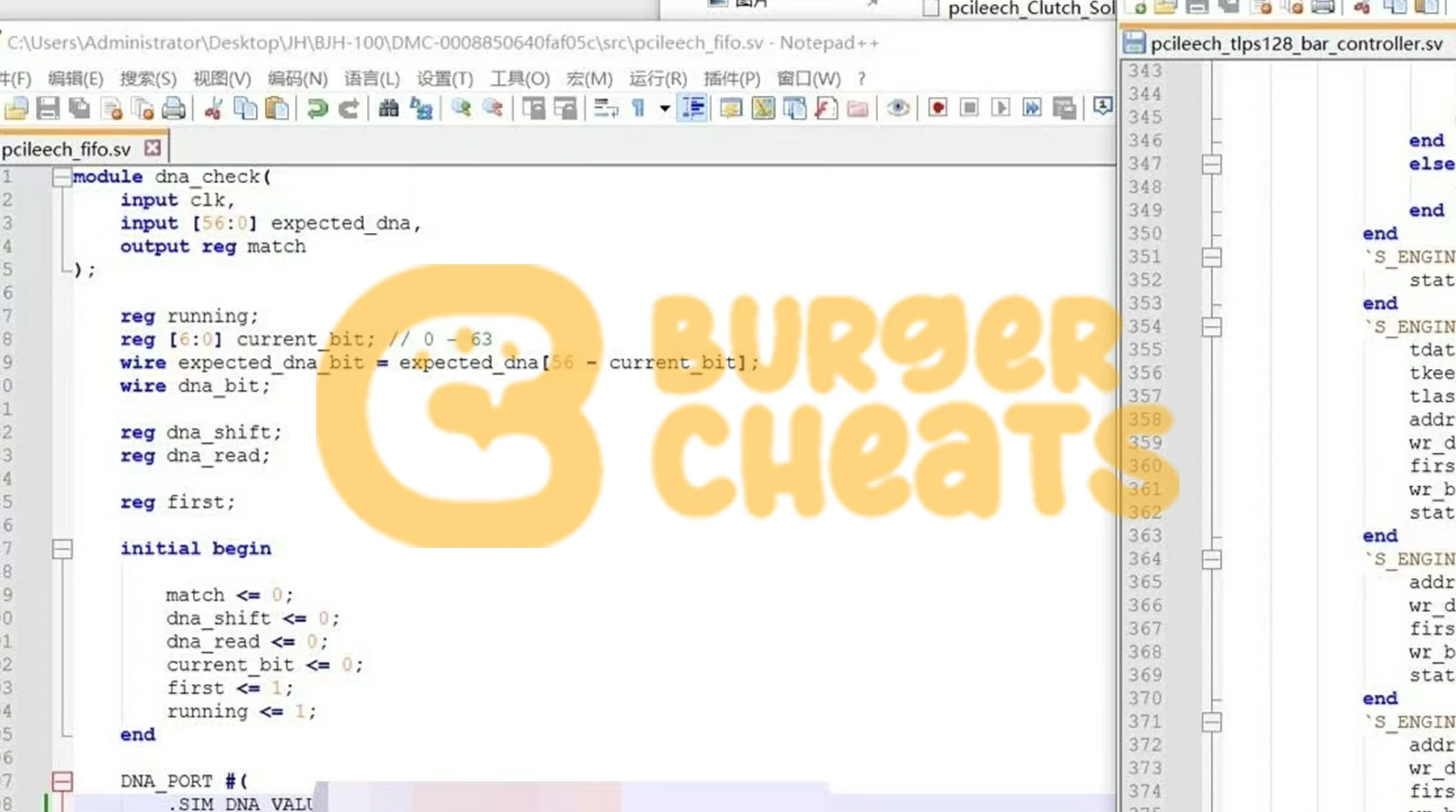
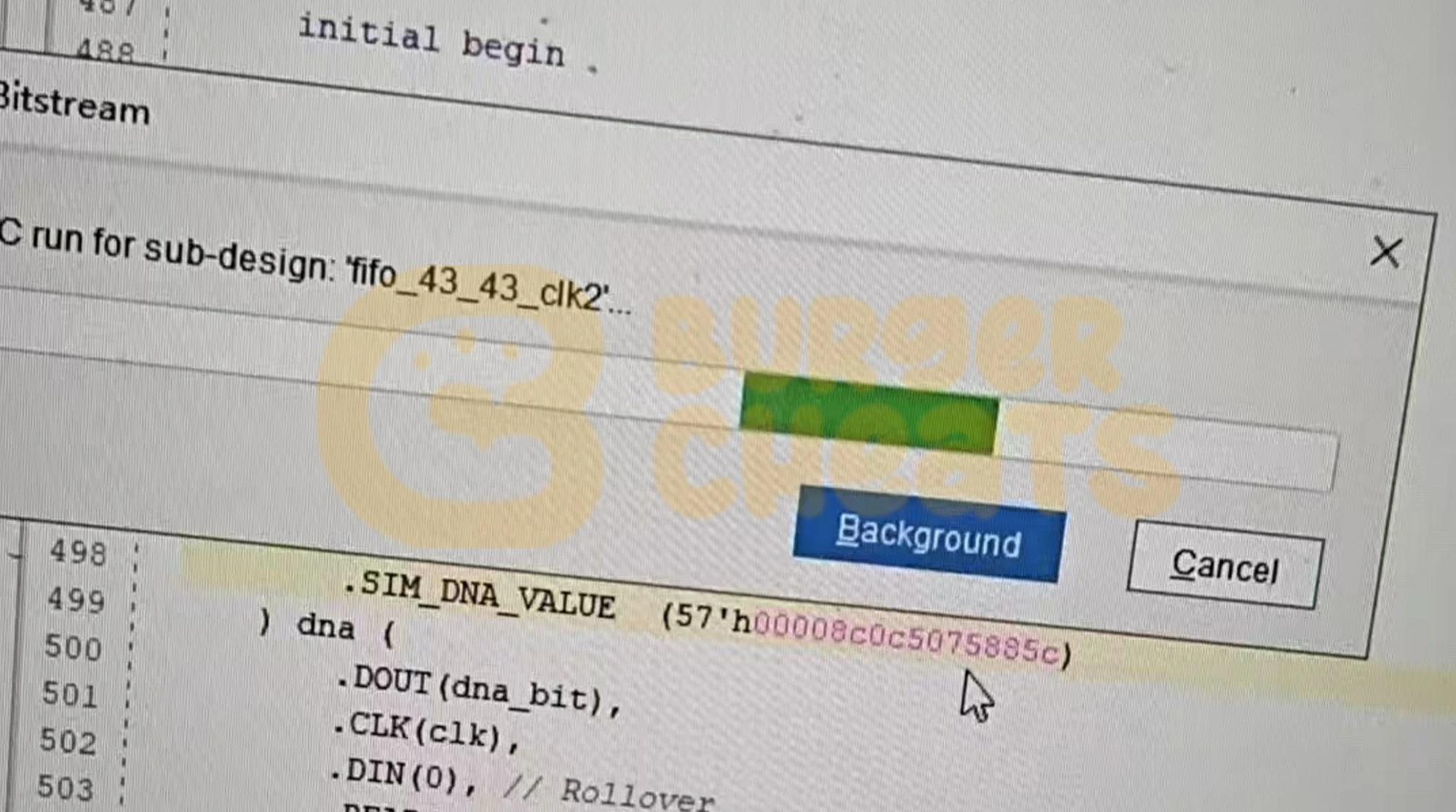
Stock pcileech firmware presents as VID=0x10EE, DID=0x0666 — the "Xilinx Ethernet Adapter," detected by every modern anti-cheat. Commercial vendors modify two key files:
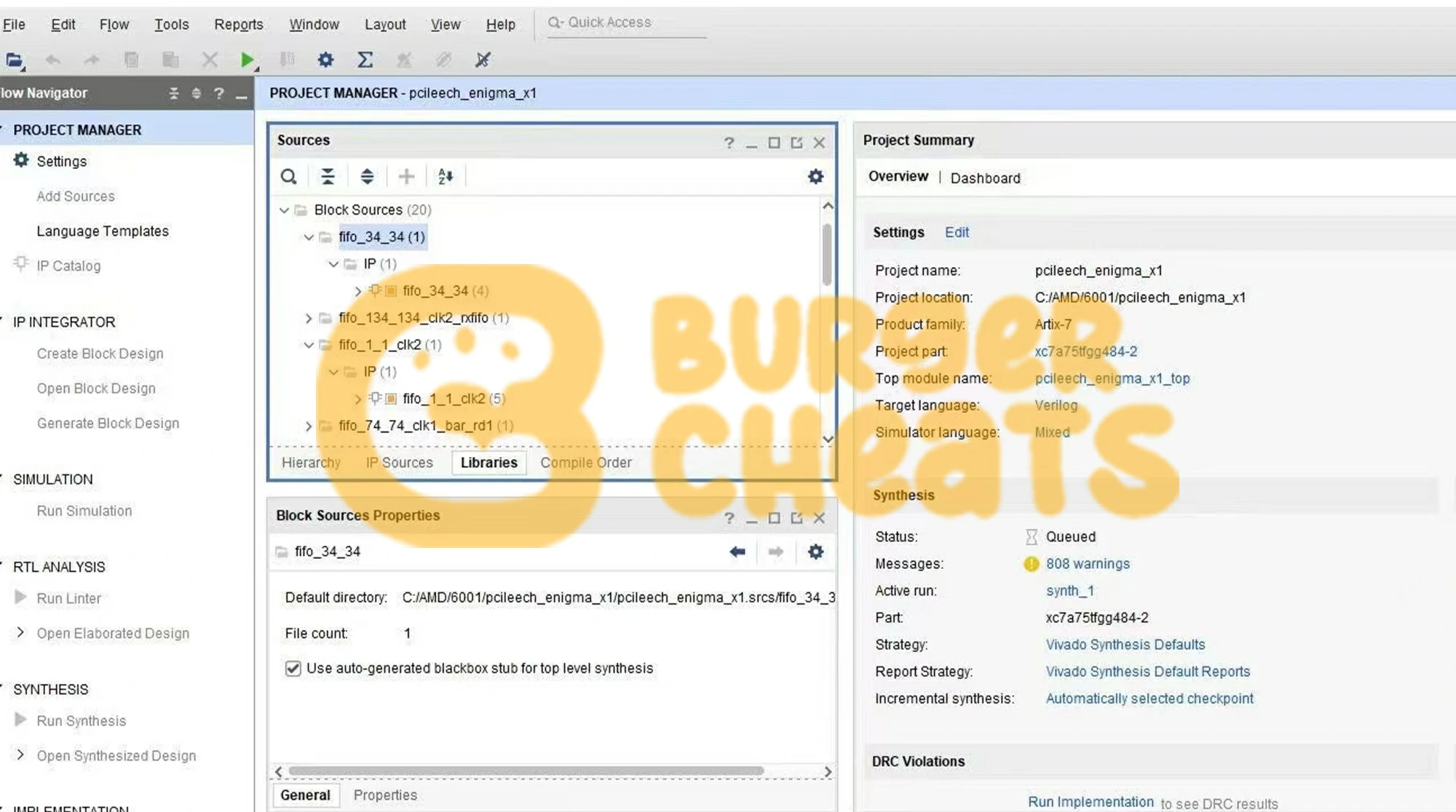
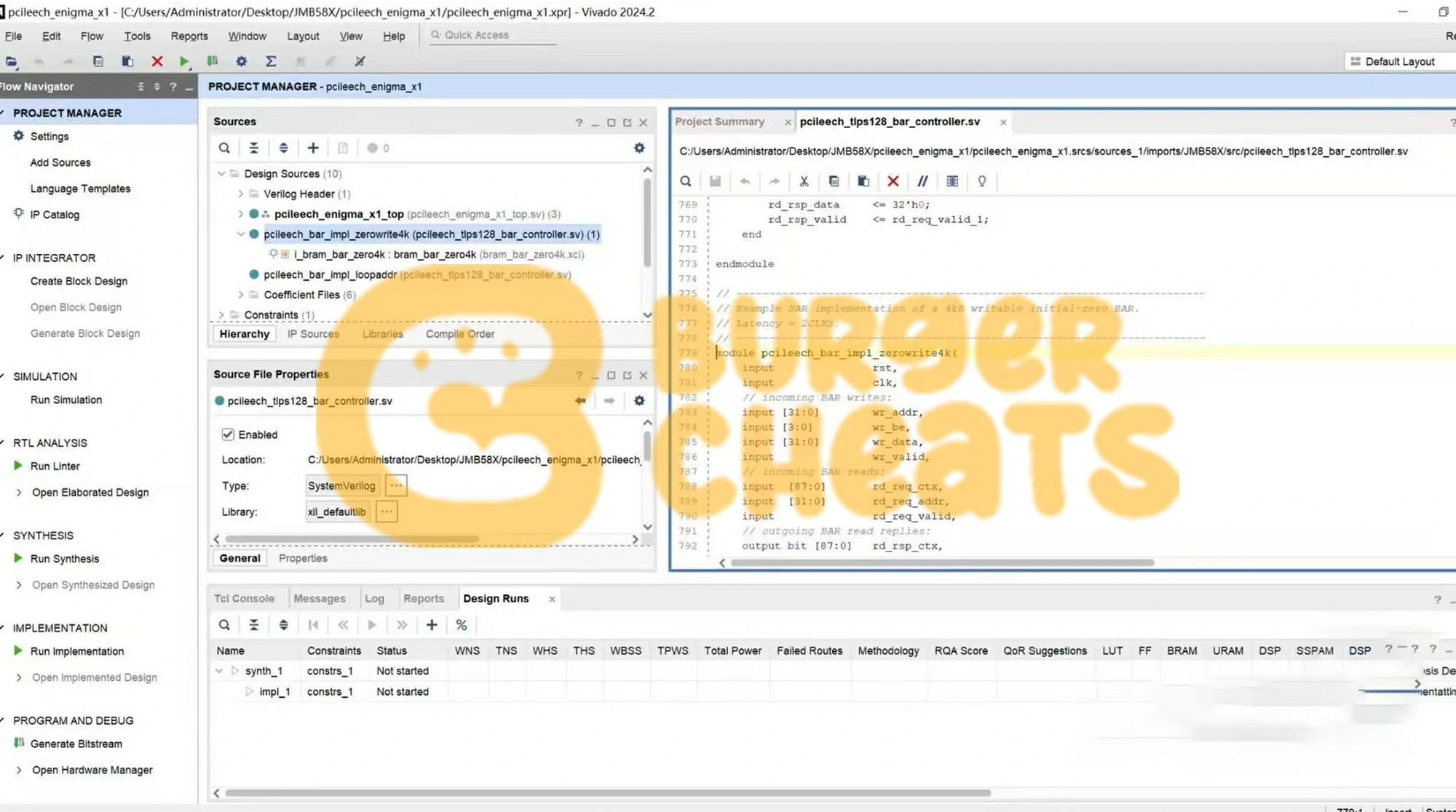
pcileech_pcie_cfg_a7.sv(the SystemVerilog config space module) andpcileech_cfgspace.coe(the BRAM initialization hex). Better vendors implement shadow BRAM, overlay RAM, and PIO logic. Budget vendors patch two hex values in Vivado's GUI and call it "custom."The Vivado Build Pipeline
Every firmware build follows the same compilation flow regardless of vendor. Synthesis converts the modified SystemVerilog/Verilog HDL into a gate-level netlist. Implementation maps that netlist to the target FPGA's physical resources — placing logic cells, routing interconnects, configuring BRAM tiles. Bitstream generation produces the .bit file that programs the FPGA. Flashing writes the bitstream to the card via USB-JTAG (CH347 programmer for 75T boards, or built-in USB on Screamer-type devices). The full Vivado synthesis-to-bitstream cycle takes 15–90 minutes depending on design complexity and host CPU power.
Open-source guides like Silverr12's DMA-CFW-Guide (1,005 GitHub stars) document this entire process step by step. As the author put it: "I don't like that there are people intentionally being vague, keeping information secret, or even misleading people to drive them away from being able to make their own firmware so that they end up buying 100s of dollars worth of custom firmware from other providers with no way to guarantee quality." A 2025 ElitePVPers investigation confirmed the problem — sellers were shipping identical firmware binaries (same hash) to multiple customers while advertising "1:1 custom" builds.

Firmware Lifespan and Replacement Cadence
Firmware doesn't expire on a timer. It needs replacing when an anti-cheat pushes an update that detects the specific emulation patterns your build uses. In practice, the industry standard lifespan is 3–5 months. Aggressive anti-cheats like Vanguard can force replacements much faster — seven detection updates in 2025, each targeting different techniques. Budget for ongoing firmware costs, not a one-time purchase.
Common Misconceptions
"DMA is undetectable"
Six major ban waves in 2025 proved otherwise. Firmware protects the hardware identity layer — one layer in a multi-layer detection stack. Behavioral analysis (inhuman aim patterns, impossible reaction times), memory write detection (especially with honeypotted regions), manual review triggered by player reports, and IOMMU enforcement are all separate surfaces that firmware doesn't touch.
"1:1 custom means unique to each buyer"
It should. But community investigations found sellers shipping pooled firmware — the same binary to every customer. The PaulyUD/BossCFW operation was caught doing exactly this before exit-scamming. Most sellers refuse to hand over the .bin file, making verification impossible.
Red flag: if your firmware provider won't let you verify the build, you have no way to confirm it's actually unique.
"Cheap firmware works just as well"
Against Tier 1 anti-cheats, sometimes. Against VGK or current EAC, no. The Ditto ban wave is the clearest example: firmware that passed standard checks for months got detected by VGK and EAC within weeks of each other. Thousands of accounts lost overnight. The difference between bridge firmware and full emulation isn't marketing — it's the shadow BRAM, overlay RAM, PIO logic, and interrupt generation that survive extended validation.
What's Coming — PCIe 6.0 CMA/IDE and the Technical Endgame
The current arms race still operates within the boundaries of the existing PCIe specification, where devices are trusted by default. That changes with two features in the PCIe 6.0 specification: Component Measurement and Authentication (CMA) and Integrity and Data Encryption (IDE).
CMA requires PCIe devices to carry manufacturer-issued certificates and authenticate themselves through a cryptographic handshake before the host grants bus access. An FPGA pretending to be an Intel NIC would need Intel's private signing key — which it obviously doesn't have. IDE encrypts all traffic on the PCIe bus, making passive memory snooping impossible even if a device does gain bus access.
These features require new hardware adoption — current motherboards and devices don't support them. But they represent the definitive technical endgame for DMA. Once CMA/IDE deployment reaches critical mass (likely 3–5 years given hardware refresh cycles), the FPGA-based DMA model as it exists today becomes fundamentally unviable. The arms race doesn't end — it shifts to entirely different attack surfaces.
Frequently Asked Questions
What is the difference between Custom and Emulated DMA firmware?
Custom (bridge) firmware patches identity fields through the Xilinx IP core GUI but leaves internal config space structures at default values — detectable by modern anti-cheats. Emulated firmware implements full shadow config space in BRAM with overlay RAM for write consistency, TLP compliance, BAR response logic, and driver integration. Emulated is the minimum standard for EAC, ACE, and Vanguard in 2026.
Does DMA firmware work across different games?
The firmware disguises the DMA card at the PCIe level, below any game-specific logic. What matters is the anti-cheat: firmware validated against BattlEye will pass BattlEye regardless of the specific game. But firmware built only for BattlEye won't survive Vanguard's deeper scanning. Make sure your firmware is rated for the toughest anti-cheat in your game library.
How does DMA firmware relate to HWID spoofing?
Different layers of protection. Firmware hides the DMA card from anti-cheat hardware scans. An HWID spoofer changes your gaming PC's identifiers — disk serial, motherboard UUID, MAC address — to avoid hardware bans on your account. If you've been HWID banned, you need both. Starting fresh, firmware covers the DMA card; a spoofer is insurance against future hardware bans.
Why did so many DMA users get banned in 2025?
2025 was a detection inflection point. IOMMU enforcement blocked DMA memory access at the hardware level. VGK's honeypotted memory trapped readers. A/B functionality tests caught every common donor device class. The Sleeping Bouncer disclosure led to mandatory BIOS patches. And Remote Attestation moved boot verification to the cloud. Each of these attacked a different evasion layer — firmware alone couldn't protect against all of them simultaneously.
What FPGA chips do DMA cards use?
All major DMA cards use Xilinx (AMD) Artix-7 FPGAs. The XC7A35T (33,280 logic cells) powers entry-level boards. The XC7A75T (75,520 logic cells) is the most popular — enough resources for full emulation. The XC7A100T (101,440 logic cells) handles the most complex profiles. More logic cells = more room for shadow BRAM, overlay RAM, PIO controllers, and interrupt logic.
Is DMA cheating "dying"?
It's getting harder, more expensive, and more legally risky. The isdmadead.com timeline documents continuous detection evolution since 2017, and 2025 marked the sharpest escalation yet. On the legal front, Epic won $175K against a tournament cheater using DMA hardware, and Activision won $14.5M against EngineOwning. DMA still works — firmware complexity rises to match detection — but the cost-benefit equation has shifted: more frequent replacements, stricter system requirements (TPM, Secure Boot, IOMMU, updated BIOS), ban waves that hit harder, and the long-term threat of PCIe 6.0 CMA/IDE eliminating the attack surface entirely.
Explore BurgerCheats DMA Firmware
We build emulated 1:1 firmware with full shadow config space, overlay RAM write consistency, TLP compliance, and dedicated driver loading. Every build uses a unique donor scan and is hardware-bound to your specific DMA card. Check our current packages, supported cards, and warranty terms:
Browse DMA Firmware in the Store →
Questions about compatibility, BIOS requirements, or setup? Our team handles technical questions daily. Check the status page for real-time detection status across all supported titles.